Cybersecurity researchers have exposed a previously undocumented threat actor, TA585, which delivers an off-the-shelf malware called MonsterV2 through targeted phishing campaigns. Proofpoint researchers describe TA585 as operating a self-owned, end-to-end attack chain, managing infrastructure, delivery, and payload installation without relying on third-party distribution services.
Background and delivery methods
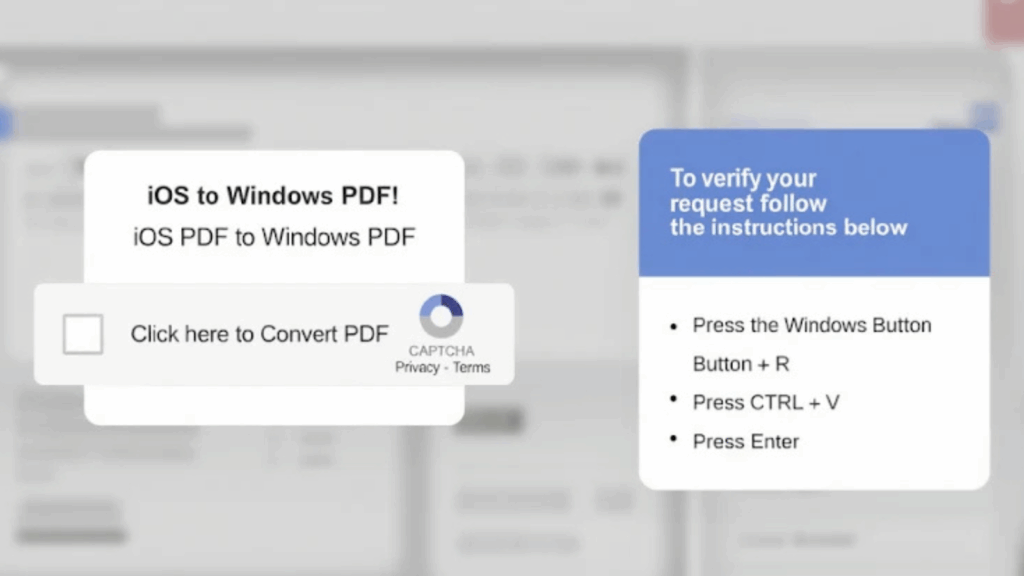
TA585 has used multiple delivery techniques in its campaigns, including phishing emails with U.S. Internal Revenue Service, IRS, themed lures. Victims are directed to a fake PDF that links to a web page using the ClickFix social engineering tactic, which coerces users into running a malicious command in the Windows Run dialog or a PowerShell terminal. That command fetches and runs a next-stage PowerShell script that installs MonsterV2.
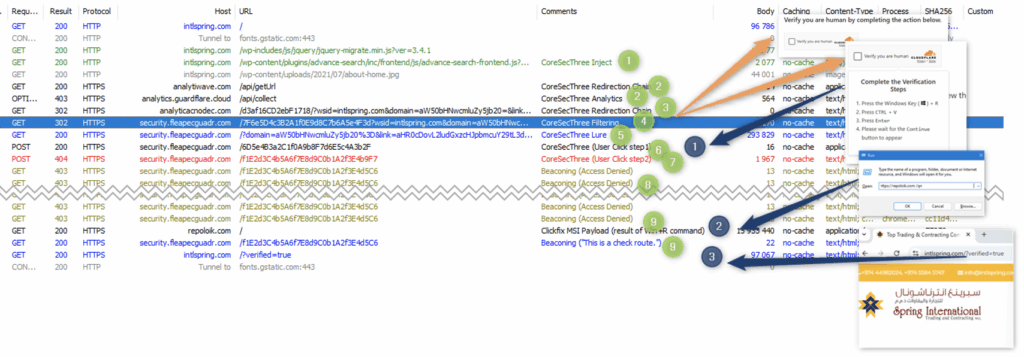
Later waves in April 2025 added malicious JavaScript injections on legitimate websites, which show fake CAPTCHA overlays to trigger ClickFix, again leading to a PowerShell command that delivers the malware. Earlier variants in these campaigns deployed Lumma Stealer, but TA585 switched to MonsterV2 in early 2025. The JavaScript inject and related infrastructure, including intlspring[.]com, have also been tied to Rhadamanthys Stealer distribution.
Another campaign variant used fake GitHub security notifications, created by tagging GitHub users in bogus alerts, which contain URLs that point to actor-controlled websites and initiate the infection chain.
Both activity clusters that use web injects and phony GitHub alerts have links to CoreSecThree, a sophisticated framework active since February 2022, which has been used consistently to distribute stealer malware.
What MonsterV2 does, core features
MonsterV2 is a multi-functional malware, combining RAT, stealer, and loader capabilities. Proofpoint observed it advertised on criminal forums in February 2025, under names that include Aurotun Stealer, a misspelling of autorun, and noted prior distribution via CastleLoader, aka CastleBot.
Key capabilities include, but are not limited to, the following:
- Infostealer functionality, to collect and exfiltrate sensitive data
- Clipper behavior, replacing cryptocurrency addresses in the system clipboard with actor-controlled wallet addresses
- Remote control via Hidden Virtual Network Computing, HVNC, allowing full interactive sessions
- Remote command execution, download and execution of additional payloads, and module management
- Screenshots, keylogging, file enumeration, manipulation and exfiltration, process control, and system shutdown or crash
MonsterV2 normally uses a C++ crypter called SonicCrypt to pack the payload, enabling anti-analysis behaviors before decrypting and loading the core module.
Technical details, configuration and C2 interaction
When run, MonsterV2 decrypts and resolves Windows API functions required for operation, attempts privilege escalation where configured, and decodes an embedded configuration that controls behavior. Notable configuration flags include, for example, anti_dbg, anti_sandbox, aurotun, and priviledge_escalation, which direct anti-debugging, anti-sandbox checks, persistence setup, and privilege escalation attempts respectively.
If the malware reaches out to its command-and-control server and establishes contact, it sends basic system information and the machine’s geolocation, using a query to api.ipify[.]org to obtain the external IP. The C2 server responds with commands that the malware executes on the host. Supported remote tasks include, but are not limited to:
- Exfiltrate stolen data to the server
- Run arbitrary commands through cmd.exe or PowerShell
- Terminate, suspend, or resume processes
- Establish an HVNC connection for remote control
- Capture desktop screenshots, start a keylogger
- Enumerate and exfiltrate files, download and execute secondary payloads such as StealC and Remcos RAT
Proofpoint noted that some MonsterV2 deployments shared C2 infrastructure with other malware, for example StealC, although that specific association was not directly attributed to TA585 in all cases.
Pricing, targeting, and evasion
MonsterV2 is offered for sale by a Russian-speaking actor, priced at about $800 USD per month for a Standard edition, and $2,000 per month for an Enterprise edition which adds features like CDP support and more advanced loaders. The stealer component is configured to avoid infecting systems in Commonwealth of Independent States, CIS, countries.
To hinder detection, the malware uses SonicCrypt and performs anti-analysis checks, sandbox detection, and other evasion techniques before payload execution.