A global malvertising operation known as TamperedChef is actively spreading malware through fake installers disguised as trusted software. Attackers are using deceptive tactics to make users download harmful programs, allowing them to establish remote access and persistent control over infected systems. Recent findings from the Acronis Threat Research Unit show that the campaign remains active, and new malicious components continue to surface.
How the TamperedChef Campaign Operates
Security researchers Darrel Virtusio and Jozsef Gegeny explain that the operators behind this campaign depend heavily on social engineering. They imitate well known software names, use search engine manipulation, run misleading advertisements, and abuse legitimate looking digital certificates to convince users that the installers are genuine.
TamperedChef refers to both the long running campaign and the information stealer malware distributed through fake installers. This activity is assessed as part of a wider threat cluster called EvilAI, which often uses artificial intelligence themed tools and utilities as bait for distributing malicious files.
To make their counterfeit applications appear authentic, the attackers sign them using certificates issued to shell companies created in regions such as the United States, Panama, and Malaysia. When older certificates lose credibility or are revoked, they simply obtain new ones under fresh company names.
Acronis describes the supporting infrastructure as highly organized and structured like a commercial operation. This setup enables the attackers to continuously produce new certificates and exploit the inherent trust that users generally place in signed applications.
Some cybersecurity firms use different names for the malware, for example BaoLoader. Acronis notes that it continues to use the name TamperedChef because the term is already widely used within the cybersecurity community, which helps avoid confusion when comparing analyses.
Attack Methodology
The attack chain usually begins when users search online for PDF editors, software manuals, or similar tools. Search engines like Bing may display malicious advertisements or poisoned links that lead to attacker controlled websites. These domains, frequently registered through NameCheap, trick visitors into downloading fake installers.
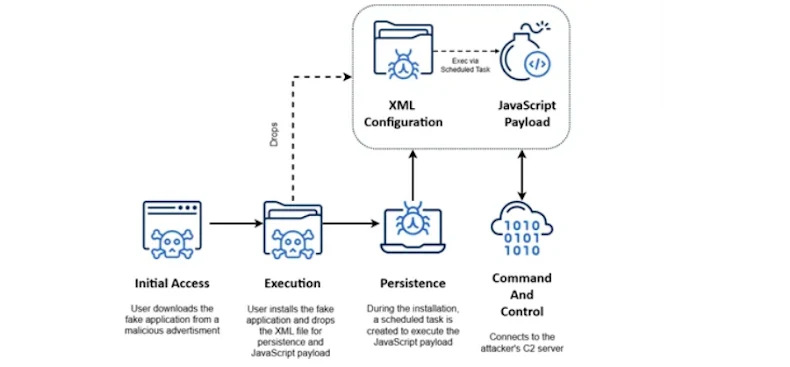
When a user runs one of these installers, they are first asked to accept licensing terms. After installation, a new browser tab appears with a thank you message, creating the impression of a normal setup process. Meanwhile, the installer secretly drops an XML file that schedules a task. This task executes an obfuscated JavaScript backdoor that maintains persistence.
Once active, the backdoor contacts a remote server and sends data such as machine identifiers, session details, and other metadata. This information is bundled into a JSON object, encrypted, encoded with Base64, and transferred over HTTPS.
Possible Motives and Global Impact
The exact purpose of the campaign is not always clear. Some variants have been observed conducting advertising fraud, which indicates a financial motivation. However, attackers may also attempt to sell system access to other criminal groups or steal sensitive data to trade on underground marketplaces.
Telemetry shows most infections have occurred in the United States, followed by Israel, Spain, Germany, India, and Ireland. Sectors such as healthcare, construction, and manufacturing appear to be the primary targets. These industries often rely on specialized technical equipment, which causes employees to frequently search online for product manuals, a behavior that the attackers specifically exploit.


