Cybersecurity experts have uncovered a large and coordinated malicious campaign that abuses cloud native environments to construct infrastructure used for cybercrime operations. Researchers describe the activity as a worm driven operation that spreads automatically across exposed cloud services.
The campaign was first observed around December 25, 2025, and relies on publicly exposed Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers. The attackers also exploit the recently disclosed React2Shell vulnerability, tracked as CVE-2025-55182 with a critical CVSS score of 10.0.
Security analysts have attributed the activity to a threat group known as TeamPCP, which is also tracked under multiple aliases including DeadCatx3, PCPcat, PersyPCP, and ShellForce.
Growing Presence of the TeamPCP Threat Group
TeamPCP has been active since at least November 2025, while its earliest known presence on Telegram dates back to July 30, 2025. The group operates a Telegram channel with more than 700 members, where it regularly publishes stolen data.
Victims affected by the campaign span multiple regions, including Canada, Serbia, South Korea, the United Arab Emirates, and the United States. The threat actor was first publicly documented in December 2025 by Beelzebub under the name Operation PCPcat.
According to Flare security researcher Assaf Morag, the primary objective of the campaign is to establish a distributed scanning and proxy infrastructure at scale. Once access is gained, compromised systems are used for data theft, ransomware deployment, extortion activities, and cryptocurrency mining.
Cloud Native Attacks at Industrial Scale
TeamPCP operates as a cloud native cybercrime platform. Instead of focusing on traditional endpoints, the group targets misconfigured cloud services and vulnerable web applications to breach modern infrastructure environments.
Compromised systems are later repurposed for multiple criminal uses, including cryptocurrency mining, data hosting, proxy services, and command and control relay networks. Researchers note that the group does not rely on advanced or novel techniques. Instead, it uses widely known vulnerabilities, existing tools, and common misconfigurations to automate attacks at scale.
This approach enables TeamPCP to convert exposed cloud infrastructure into a self propagating criminal ecosystem that continuously expands without manual intervention.
Payloads Designed for Propagation and Persistence
Once initial access is achieved, the attackers deploy additional payloads from external servers. These payloads are written in shell and Python and are designed to identify new vulnerable targets to further extend the campaign.
One of the central components of the operation is a script called proxy.sh. This script installs proxy services, peer to peer tunneling utilities, and scanning tools that actively search the internet for additional misconfigured servers.
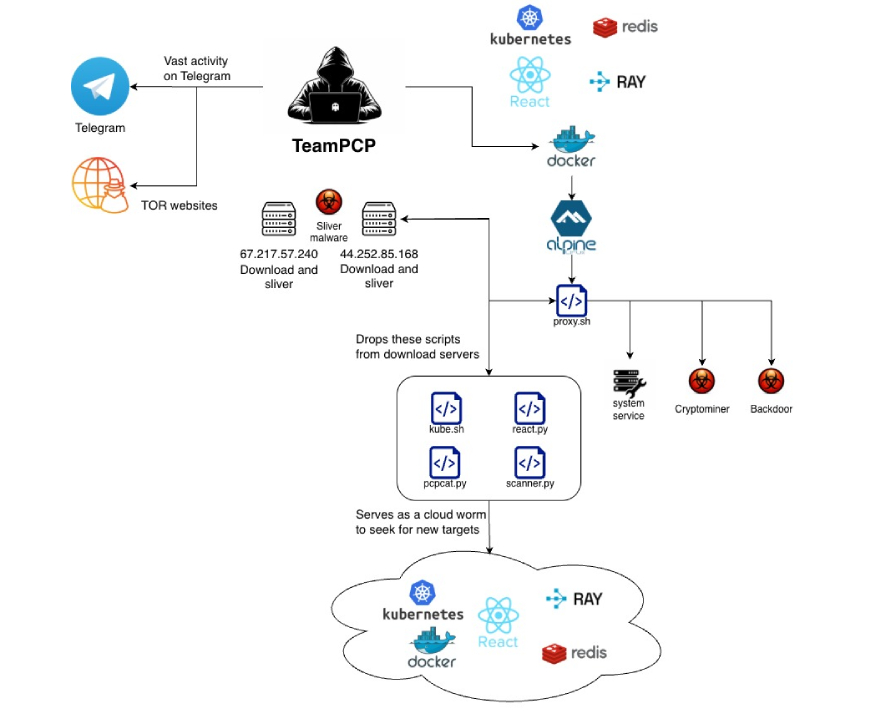
Researchers highlight that proxy.sh performs environment fingerprinting during execution. If the script detects that it is running inside a Kubernetes environment, it switches execution paths and deploys Kubernetes specific payloads. This behavior indicates that TeamPCP maintains dedicated tooling tailored for cloud native targets rather than relying solely on generic Linux malware.
Overview of Additional Malicious Components
Other payloads observed during the investigation include scanner.py, which searches for exposed Docker APIs and Ray dashboards using CIDR ranges downloaded from a GitHub account associated with DeadCatx3. This script also includes optional cryptocurrency mining functionality.
Another payload, kube.py, focuses on Kubernetes environments by harvesting credentials, enumerating cluster resources such as pods and namespaces, and deploying proxy.sh across accessible pods. It also establishes persistence by creating privileged pods on cluster nodes.
The react.py script exploits the React vulnerability CVE-2025-29927 to achieve remote command execution at scale. Meanwhile, pcpcat.py scans large IP ranges to locate exposed Docker APIs and Ray dashboards, automatically deploying malicious containers that execute encoded payloads.
Infrastructure and Targeting Patterns
Flare researchers have linked a command and control server at 67.217.57[.]240 to the operation. This server has also been associated with Sliver, an open source command and control framework commonly abused for post exploitation activities.
Analysis shows that the attackers primarily target Amazon Web Services and Microsoft Azure environments. The campaign appears to be opportunistic, focusing on exposed infrastructure rather than specific industries. As a result, many affected organizations become unintended collateral victims.
According to researchers, the PCPcat campaign demonstrates a complete attack lifecycle that includes scanning, exploitation, persistence, tunneling, data theft, and monetization, all designed specifically for modern cloud platforms.
What makes TeamPCP particularly dangerous is not technical sophistication, but the scale and integration of its operations. By combining infrastructure abuse with data theft and extortion, the group creates multiple revenue streams and increases its resilience against disruption and takedown efforts.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


