A new wave of cyber attacks linked to the threat actor known as Tomiris has been identified targeting foreign ministries, intergovernmental bodies, and government institutions inside Russia. According to researchers, the actor aims to gain remote access inside sensitive networks and deploy additional malicious tools for long term operations.
Kaspersky analysts Oleg Kupreev and Artem Ushkov reported a major shift in Tomiris tactics, stating that the group is increasingly relying on implants that use public platforms such as Telegram and Discord as command and control servers. This strategy blends malicious communication with routine traffic from popular services, which makes detection far more difficult for security systems.
Investigators found that over half of the spear phishing emails and decoy documents used in this campaign were written in Russian and contained Russian names. This suggests a strong focus on Russian speaking targets. However, similar attacks were also directed at Turkmenistan, Kyrgyzstan, Tajikistan, and Uzbekistan using messages crafted in each country’s local language.
Use of Multi Stage Malware for Political and Diplomatic Espionage
The attacks against high value political and diplomatic networks used a chain of techniques that included reverse shells, custom implants, and open source frameworks such as Havoc and AdaptixC2 to support post exploitation activity.
Tomiris was first documented in 2021 when Kaspersky analyzed a backdoor with the same name. Researchers noted similarities with SUNSHUTTLE, also called GoldMax, which was used by the APT29 group in the SolarWinds supply chain attack. Additional overlaps were seen with Kazuar, a .NET espionage malware linked to Turla. Despite these technical connections, investigators assess Tomiris as a separate threat actor, primarily collecting intelligence in Central Asia. Microsoft later associated the Tomiris backdoor with a Kazakhstan based actor called Storm 0473.
Further analysis by Cisco Talos, Seqrite Labs, Group IB, and BI.ZONE supported this assessment. Their reports highlighted similarities with clusters known as Cavalry Werewolf, ShadowSilk, Silent Lynx, SturgeonPhisher, and YoroTrooper.
Attack Chain Begins with Phishing Emails
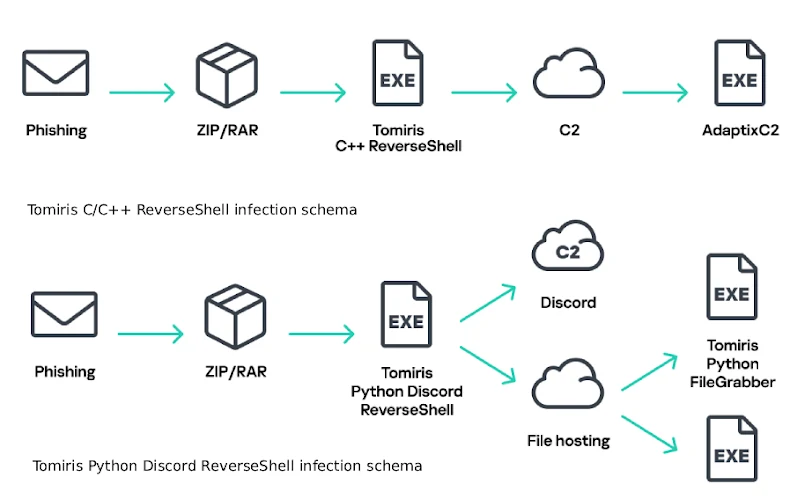
Kaspersky observed that the most recent campaign begins with phishing emails that contain password protected RAR archives. The required password is included inside the email message. When opened, the archive reveals an executable that pretends to be a Microsoft Word document, using the extension .doc.exe. Once launched, it installs a C and C plus plus reverse shell that collects system information and connects to a command server to download AdaptixC2.
The reverse shell also modifies Windows Registry settings to maintain persistence. Kaspersky identified three different versions of this malware family during the current year.
Alternate Infection Pathways Using Rust, Python, and Other Languages
Some archives delivered additional malware families that each started their own infection sequence. These included:
• A Rust based downloader that gathers system information and transmits it to a Discord webhook. It creates VBScript and PowerShell files, then runs a VBScript via cscript to execute the PowerShell script. The script downloads a ZIP file containing an executable linked to the Havoc framework.
• A Python based reverse shell that uses Discord for command and control. It executes commands, carries out reconnaissance, and retrieves implants such as AdaptixC2 and a Python based FileGrabber capable of collecting files with jpg, png, pdf, txt, docx, and doc extensions.
• A Python based backdoor named Distopia, built using the open source dystopia-c2 project. It relies on Discord for command and control. This malware downloads additional payloads including a Python reverse shell that uses Telegram for command execution and returns the output to the server.
A Diverse Arsenal of Multi Language Implants
Tomiris employs a wide variety of reverse shells and implants written in different programming languages. These include:
• A C sharp reverse shell that uses Telegram to receive and run commands
• Rust based malware called JLORAT that executes commands and captures screenshots
• A Rust reverse shell that uses PowerShell instead of cmd.exe
• A Go based reverse shell that uses TCP connections to run commands through cmd.exe
• A PowerShell backdoor that receives instructions through Telegram and downloads any file to the C:\Users\Public\Libraries\ folder
• A second C sharp reverse shell that uses a TCP connection for executing commands via cmd.exe
• A reverse SOCKS proxy in C plus plus that modifies the open source Reverse SOCKS5 project by removing debug messages and hiding the console
• A Golang based reverse SOCKS5 proxy that similarly removes debugging output and conceals the console window
Kaspersky concluded that the Tomiris 2025 operation demonstrates a deliberate use of malware written in multiple programming languages to increase flexibility and avoid detection. This evolution shows the group’s long term focus on stealth, persistence, and intelligence collection against government and intergovernmental organizations.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


