A recent spear-phishing operation, named PhantomCaptcha, has targeted organizations involved in Ukraine’s humanitarian and war relief efforts. Cybersecurity researchers reported that the campaign delivers a remote access trojan (RAT) using WebSocket connections for command-and-control (C2), posing a serious threat to international relief organizations.
Scope of the Attack
On October 8, 2025, individual members of the International Red Cross, Norwegian Refugee Council, UNICEF Ukraine office, Council of Europe’s Register of Damage for Ukraine, and Ukrainian regional governments in Donetsk, Dnipropetrovsk, Poltava, and Mikolaevsk were targeted, according to SentinelOne.
Methodology
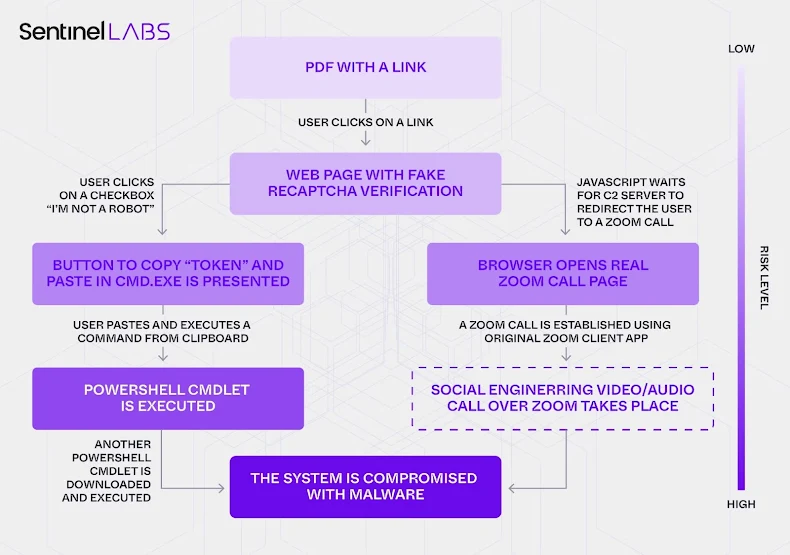
The phishing emails impersonated the Ukrainian President’s Office and included a malicious PDF with an embedded link. When clicked, victims are redirected to a counterfeit Zoom site (“zoomconference[.]app”) and prompted to execute a malicious PowerShell command via a fake Cloudflare CAPTCHA page resembling ClickFix.
This fake CAPTCHA page serves as a bridge, establishing a WebSocket connection with an attacker-controlled server. A JavaScript-generated clientId is transmitted, and the browser only navigates to a legitimate, password-protected Zoom meeting if the WebSocket server validates the identifier.
Payload Delivery and Execution
The executed PowerShell command downloads a second-stage malware payload. This stage performs reconnaissance on the infected host and communicates data back to the attack server, which subsequently delivers the WebSocket RAT. This RAT provides full remote control, enabling arbitrary command execution, data exfiltration, and deployment of additional malware.
Technical Details
The malware connects to “wss://bsnowcommunications[.]com:80,” receiving Base64-encoded JSON commands executed via Invoke-Expression or PowerShell scripts. Results are sent back in JSON format over the WebSocket connection.
VirusTotal submissions show that the 8-page weaponized PDF originated from Ukraine, India, Italy, and Slovakia, highlighting broad targeting. Preparations for the campaign began on March 27, 2025, with the domain “goodhillsenterprise[.]com,” serving obfuscated PowerShell scripts. The Zoom site infrastructure was only active on October 8. Additionally, fake Android apps hosted on “princess-mens[.]click” were designed to harvest geolocation, contacts, call logs, media, device info, and installed apps.