In early 2025, a covert cyber-espionage campaign targeted diplomats and government organizations across Southeast Asia and other regions.
At the core of this operation is STATICPLUGIN, a downloader cleverly disguised as a legitimate Adobe plugin update.
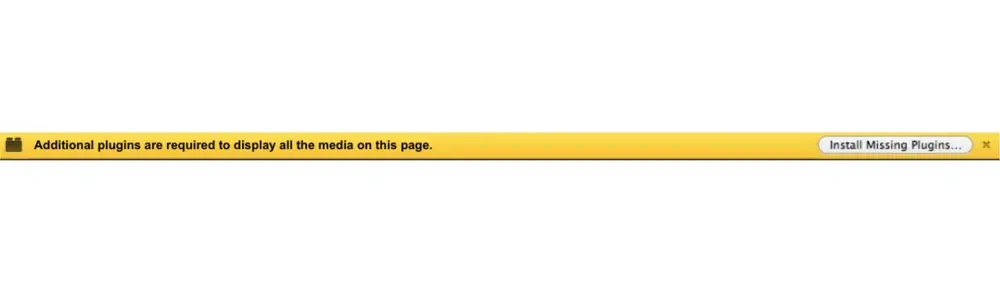
Malicious Redirect via Captive Portal
Victims experienced a captive portal hijack, redirecting browsers to malicious domains. The landing page, secured with HTTPS, prompted users to “Install Missing Plugins…”, a deceptive tactic designed to bypass browser warnings and lower suspicion.
When executed, STATICPLUGIN initiates a multi-stage chain culminating in the in-memory execution of the SOGU.SEC backdoor.
Multi-Stage Payload Delivery
STATICPLUGIN downloads an MSI package disguised as a BMP image. Inside, CANONSTAGER is side-loaded as a DLL to run the encrypted payload cnmplog.dat. This technique exploits trusted Windows components to evade host defenses.
Security analysts at Google Cloud highlighted this unique combination of captive portal hijacking and valid code signing as a sophisticated evolution in PRC-linked cyber tradecraft.
Certificates issued by Chengdu Nuoxin Times Technology Co., Ltd., and signed via GlobalSign and Let’s Encrypt, lent STATICPLUGIN a false legitimacy, allowing it to bypass many endpoint security solutions.
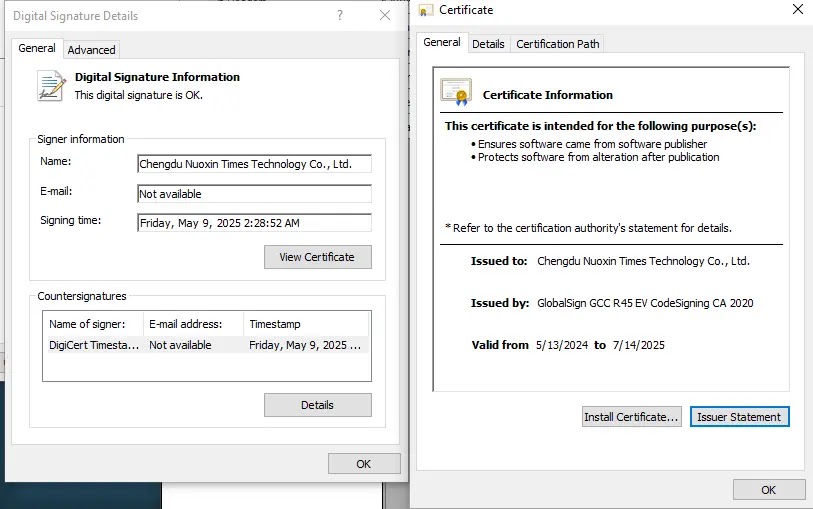
Although the original certificate expired on July 14, 2025, UNC6384 likely re-signs new builds to maintain continuous stealth.
Advanced Evasion Techniques
CANONSTAGER uses unconventional methods to hide its operations. It resolves Windows API addresses through a custom hashing algorithm and stores them in Thread Local Storage (TLS), an unusual location overlooked by standard monitoring tools.
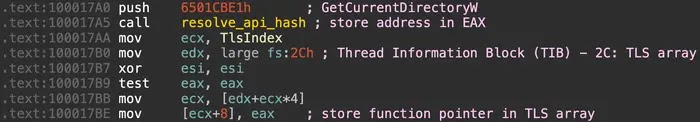
By triggering these functions via a hidden window procedure and dispatching WM_SHOWWINDOW messages, CANONSTAGER masks its control flow within legitimate Windows message queues.
Detection Evasion with In-Memory Execution
One of UNC6384’s notable innovations is fully in-memory execution. CANONSTAGER creates a thread to decrypt cnmplog.dat using a hardcoded 16-byte RC4 key.
Instead of writing the payload to disk, it executes SOGU.SEC directly in memory using EnumSystemGeoID as a callback. This removes forensic artifacts and prevents traditional endpoint detection.
Communications with the C2 server at 166.88.2.90 are conducted over HTTPS, blending with regular traffic to evade network-based monitoring.
The initial JavaScript triggers AdobePlugins.exe, setting the stage for in-memory execution. By bypassing disk writes and using legitimate certificates, UNC6384 demonstrates advanced malware stealth techniques.
Recommendations for Defenders
- Inspect memory artifacts for unusual activity
- Enforce strict code-signing policies
- Enable Enhanced Safe Browsing to detect suspicious TLS certificates and captive portal hijacks