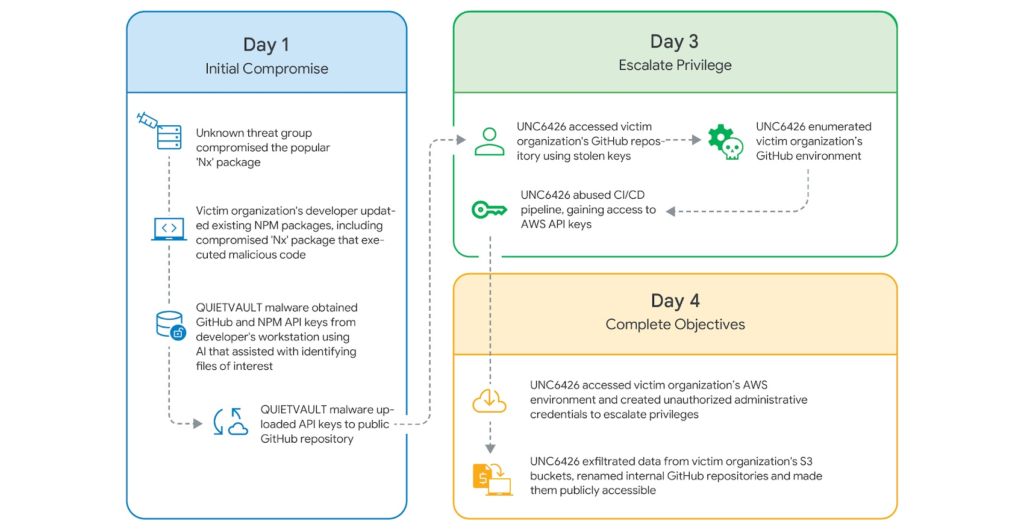
Cybersecurity investigators have revealed that a threat actor identified as UNC6426 successfully breached a company’s cloud infrastructure within 72 hours by abusing credentials stolen during a software supply chain compromise involving the Nx npm package.
According to findings published in the Google Cloud Threat Horizons Report H1 2026, the attacker initially obtained a developer’s GitHub token. This credential enabled unauthorized entry into the organization’s development environment and ultimately allowed the attacker to escalate privileges inside its cloud infrastructure.
Initial Supply Chain Breach
The root of the attack traces back to August 2025, when threat actors compromised the Nx npm package using a workflow vulnerability known as Pwn Request. By exploiting a misconfigured pull_request_target GitHub workflow, attackers obtained elevated permissions that allowed them to inject malicious code into distributed versions of the package.
The modified package contained a malicious post-install script that executed a credential-stealing tool named QUIETVAULT. This malware collected sensitive information from developer systems, including environment variables, system details, and authentication tokens.
Among the data targeted were:
- GitHub Personal Access Tokens (PATs)
- environment variables
- system metadata
- CI/CD authentication secrets
The stolen data was uploaded to a public repository called /s1ngularity-repository-1 on GitHub.
AI-Assisted Credential Harvesting
The attack used an unusual technique involving a large language model tool already installed on the compromised endpoint. Instead of directly scanning the system through traditional malware logic, the malicious script instructed the AI tool to search the developer environment for sensitive information.
This approach enabled attackers to leverage the AI assistant’s access to files, credentials, and authenticated services.
Expanding Access Into AWS
Two days after the initial compromise, the attacker began reconnaissance activities inside the victim’s GitHub environment using the stolen token.
The threat actor used a legitimate open-source tool called Nord Stream to extract secrets from CI/CD environments. During this process, credentials belonging to a GitHub service account were discovered.
Using those credentials, the attacker generated temporary authentication tokens through AWS Security Token Service. This allowed access to a cloud role associated with Actions-CloudFormation, enabling deeper entry into the victim’s cloud infrastructure hosted on Amazon Web Services.
Privilege Escalation to Full Administrator
The compromised role had excessive permissions. The attacker deployed a malicious AWS CloudFormation stack with the permissions:
- CAPABILITY_NAMED_IAM
- CAPABILITY_IAM
The stack created a new IAM role and attached the AdministratorAccess policy to it.
This misconfiguration allowed the attacker to escalate from a stolen GitHub token to full cloud administrator privileges in under 72 hours.
Data Theft and Infrastructure Damage
Once administrative access was established, the attacker performed several destructive and reconnaissance actions, including:
- accessing objects stored in Amazon S3 buckets
- terminating instances in Amazon EC2
- deleting or affecting databases in Amazon RDS
- decrypting application secrets
In the final stage of the breach, the attacker renamed all internal GitHub repositories to /s1ngularity-repository-[randomcharacters] and changed their visibility to public.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


