The threat cluster known as UnsolicitedBooker has expanded its targeting footprint, moving from earlier operations in Saudi Arabia to telecommunications providers in Kyrgyzstan and Tajikistan. Security researchers report that the campaign involves two custom backdoors, LuciDoor and MarsSnake, deployed through carefully crafted phishing operations.
According to findings released by Positive Technologies, the attackers relied on uncommon tools believed to be of Chinese origin, suggesting a potential regional alignment.
Background and Links to Earlier Campaigns
UnsolicitedBooker was initially documented by ESET in May 2025, when it was linked to an intrusion against an international organization in Saudi Arabia involving the MarsSnake backdoor. Analysts assess that the group has been active since at least March 2023, with victims spanning Asia, Africa, and the Middle East.
Further investigation revealed tactical similarities with other clusters, including Space Pirates, as well as a separate Saudi focused campaign that used a backdoor known as Zardoor.
Kyrgyzstan Campaign, LuciDoor Deployment
In late September 2025, attackers targeted organizations in Kyrgyzstan through phishing emails containing malicious Microsoft Office documents. When opened, victims were prompted to Enable content, triggering a macro execution.
Although the document displayed what appeared to be a legitimate telecom tariff plan, the embedded macro secretly installed a C plus plus based loader called LuciLoad. This loader subsequently delivered the LuciDoor backdoor onto the compromised system.
A similar method was observed in November 2025, but this time a different loader, MarsSnakeLoader, was used to install the MarsSnake implant instead.
Tajikistan Attacks and Infrastructure Evolution
By January 2026, the threat actor shifted tactics slightly while targeting companies in Tajikistan. Instead of attaching malicious documents directly, phishing emails embedded links to decoy files hosted remotely. Once accessed, the infection chain followed a comparable pattern.
LuciDoor, developed in C plus plus, establishes communication with a command and control server, collects system metadata, encrypts the data, and exfiltrates it. It also executes remote commands via cmd.exe, writes files, and uploads data as instructed by the operator.
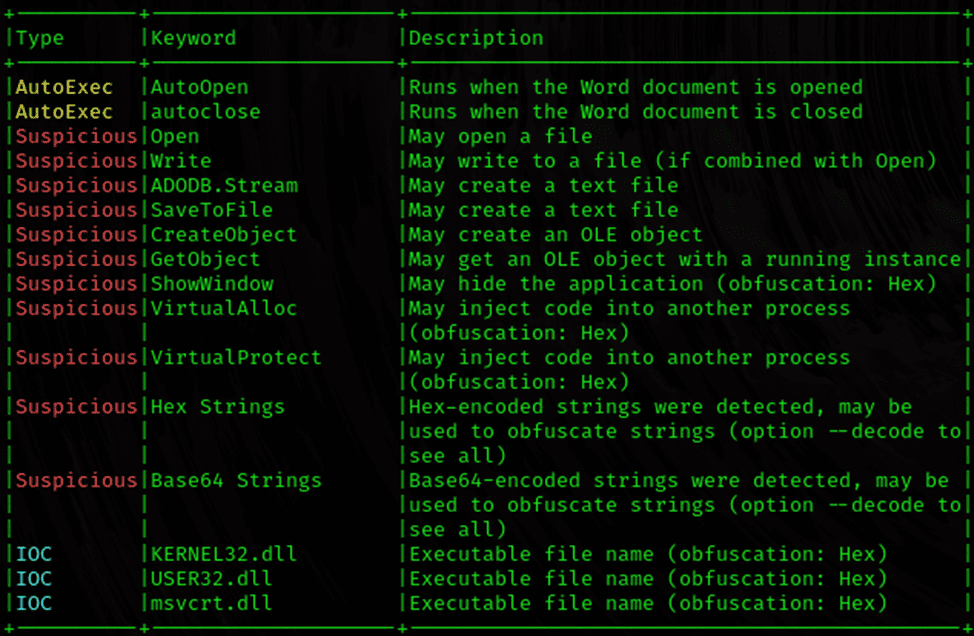
MarsSnake offers similar capabilities, including system reconnaissance, arbitrary command execution, and full file read and write access.
Researchers from Positive Technologies also identified evidence suggesting MarsSnake had previously been used in attacks targeting China.
Use of LNK Files and Tool Reuse
One infection chain leveraged a Windows shortcut file disguised as a Microsoft Word document with a doc.lnk extension. This shortcut executed a batch script that launched a Visual Basic Script, ultimately deploying MarsSnake without a loader component.
The LNK file appeared to be based on FTPlnk_phishing, a publicly available penetration testing utility, due to matching creation timestamps and machine identifiers. Notably, a comparable LNK artifact was previously used by the Mustang Panda group during operations targeting Thailand in 2022.
Positive Technologies reported that the attackers initially relied on LuciDoor, later transitioned to MarsSnake, and then reverted to LuciDoor again in 2026. In at least one case, a compromised router was repurposed as a command and control server, while parts of the infrastructure were configured to resemble Russian origin networks.
PseudoSticky Mimics Sticky Werewolf
In parallel developments, a newly identified threat actor dubbed PseudoSticky has been observed impersonating the pro Ukrainian hacking collective Sticky Werewolf, also known as Angry Likho, MimiStick, and PhaseShifters.
Active since November 2025, PseudoSticky has targeted Russian organizations in retail, construction, and research sectors. The group distributes malware such as RemcosRAT and DarkTrack RAT through phishing attachments, enabling data theft and remote system control.
Security vendor F6 noted that despite superficial similarities, infrastructure and operational techniques differ significantly, indicating deliberate imitation rather than direct affiliation.
Cloud Atlas Exploits Legacy Microsoft Word Vulnerability
Russian organizations have also faced attacks from the Cloud Atlas group, which uses phishing emails carrying malicious Word documents to deliver custom malware known as VBShower and VBCloud.
According to researchers at Solar, the malicious document loads a remote template from a command and control server. This template exploits CVE-2018-0802, a known memory corruption flaw in Microsoft Word. Following exploitation, an alternate data stream is used to download the VBShower payload.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.