A China aligned threat actor tracked as UTA0388 has run multiple spear phishing campaigns across North America, Asia, and Europe, with the main aim of delivering a Go based implant known as GOVERSHELL. Volexity reported these operations on Wednesday, noting that initial messages impersonated senior researchers and analysts from fabricated organizations, to trick recipients into clicking links that led to archives containing malicious payloads.
How the campaigns worked
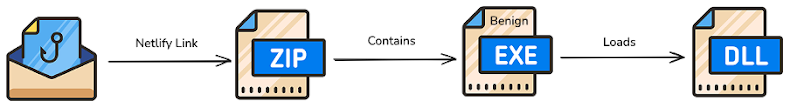
Early waves embedded links to phishing pages hosted on cloud services or on actor controlled infrastructure, which then delivered a compressed archive, usually ZIP or RAR. Later waves moved to more targeted, rapport building phishing, where the actors cultivated trust with victims over time before sending the malicious link. Regardless of method, the archive typically contains a rogue DLL that is executed via DLL side loading, which in turn launches the GOVERSHELL backdoor.
Many legitimate services were abused to host the staged archives, including Netlify, Sync, and OneDrive, while emails were observed coming from Proton Mail, Microsoft Outlook, and Gmail. The actor used multiple languages, including English, Chinese, Japanese, French, and German, and adopted a variety of fake personas to increase credibility.
GOVERSHELL, its predecessors, and variants
Volexity links this activity to an earlier C++ family called HealthKick, and Proofpoint associates similar activity under the cluster name UNK_DropPitch. Five distinct GOVERSHELL variants have been identified to date, each with different capabilities and first observed dates, as follows,
- HealthKick, first seen April 2025, capable of running commands via cmd.exe,
- TE32, first seen June 2025, uses a PowerShell reverse shell to execute commands directly,
- TE64, first seen early July 2025, runs native and dynamic commands with PowerShell, retrieves system information, checks system time, runs commands through powershell.exe, and polls a remote server for instructions,
- WebSocket, first seen mid July 2025, executes a PowerShell command through powershell.exe and contains an unimplemented update sub command in the system command,
- Beacon, first seen September 2025, runs native and dynamic commands using PowerShell, sets and randomizes a base polling interval, or executes a PowerShell command via powershell.exe.
Notable tradecraft and use of AI
A striking detail in UTA0388’s tradecraft is the use of OpenAI ChatGPT to create phishing content in English, Chinese, and Japanese, to assist malicious workflows, and to search for public tools such as nuclei and fscan. ChatGPT accounts used by the actor have been banned. Volexity assessed with medium confidence that the actor automated parts of the operation, via LLMs or other automation, sometimes sending content with little or no human oversight. The fabricated personas and occasional incoherence in message text are consistent with automated content generation.
Related targeted activity in Europe
Around the same time, StrikeReady Labs reported a suspected China linked campaign targeting a Serbian government aviation department, plus European institutions in Hungary, Belgium, Italy, and the Netherlands. That operation used phishing links that redirected victims to a fake Cloudflare CAPTCHA page, which then delivered a ZIP archive containing a Windows shortcut LNK file. The LNK executed PowerShell to open a decoy document while stealthily launching PlugX through DLL side loading.
Conclusion and recommendations
UTA0388 demonstrates an evolution from the earlier HealthKick family to the actively developed GOVERSHELL implant, with multiple variants that expand capabilities and persistence techniques. Organizations should assume targeted spear phishing is likely, and take steps including,
- Enforce strong email filtering and block known malicious hosts,
- Harden attachment handling, disallow automatic execution of archives and shortcuts,
- Monitor for DLL side loading indicators, unusual use of cmd.exe or PowerShell, and unexpected polling to remote servers,
- Provide targeted phishing awareness training, especially around rapport building tactics, and
- Investigate and block abuse of legitimate hosting services where possible.


