Cybersecurity researchers have uncovered a malicious extension for Microsoft’s Visual Studio Code (VS Code) that contains basic ransomware functionality. The extension, which appears to have been “vibe-coded” or created with the assistance of artificial intelligence, highlights a new frontier in software supply chain threats.
A Brazenly Malicious Extension
Discovered by Secure Annex researcher John Tuckner, the extension named “susvsex” was uploaded to the official VS Code Marketplace on November 5, 2025, by a user named “suspublisher18.” Remarkably, the extension made little effort to conceal its harmful intent.
Its public description explicitly stated: “Just testing. Automatically zips, uploads, and encrypts files from C:\Users\Public\testing (Windows) or /tmp/testing (macOS) on first launch.” Microsoft removed the extension from its marketplace on November 6, 2025.
How the Ransomware Extension Operates
The extension was programmed to automatically activate upon any event, such as installation or when launching VS Code. It would then execute a function called “zipUploadAndEncrypt.” This function performed a triple threat:
- Created a ZIP archive of a target directory.
- Exfiltrated the archive to a remote server.
- Replaced the original files with encrypted versions, effectively holding them for ransom.
Fortunately, the target directory was set to a test folder, limiting immediate damage. However, Tuckner warned that the target path could be easily updated in a new version or via a remote command.
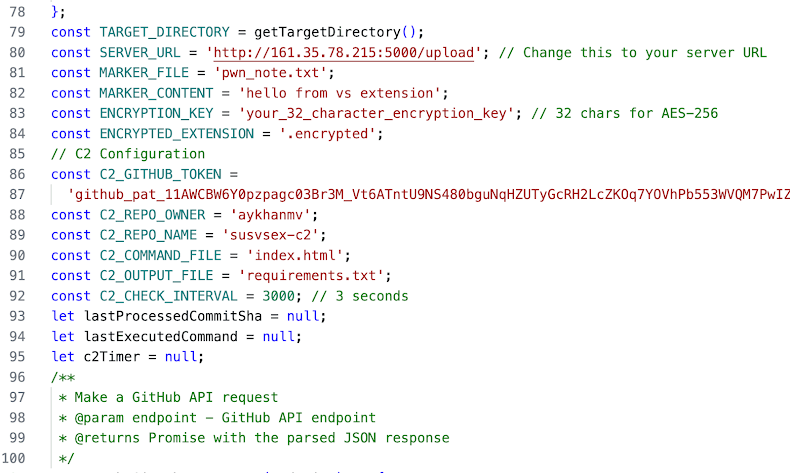
Unconventional Command-and-Control via GitHub
A key finding was the extension’s use of GitHub as its command-and-control (C2) server. The malware would periodically poll a private GitHub repository, parsing its “index.html” file for new commands to execute.
The results of these commands were then written back to the same repository in a file named “requirements.txt” using a GitHub access token hardcoded into the extension. The associated GitHub account, “aykhanmv,” remained active at the time of discovery.
The Hallmarks of “Vibe-Coded” Malware
The extension exhibited clear signs of being AI-assisted or “vibe-coded.” These indicators included extraneous comments detailing functionality, README files with execution instructions, and placeholder variables. Most critically, the package accidentally included decryption tools, C2 server code, and the GitHub access keys, which could have allowed others to hijack the attacker’s own infrastructure.
Parallel Threat: Vidar Infostealer in Trojanized npm Packages
In a related software supply chain threat, Datadog Security Labs uncovered 17 malicious npm packages posing as legitimate software development kits (SDKs). This campaign, tracked as MUT-4831, marks the first time the dangerous Vidar Infostealer has been distributed via the npm registry.
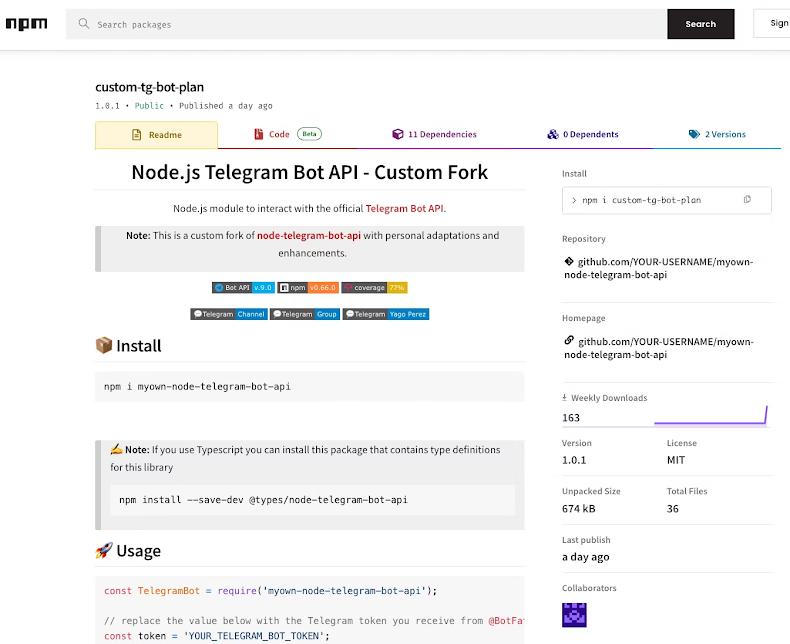
The packages, published by accounts “aartje” and “saliii229911,” were downloaded over 2,240 times before being taken down. The attack triggered through a postinstall script that downloaded a ZIP archive from a malicious domain (“bullethost[.]cloud”) and executed the Vidar stealer contained within.


