Recent research has revealed that more than 100 Visual Studio Code (VS Code) extensions have inadvertently leaked access tokens, creating a critical risk in the software supply chain. Malicious actors could exploit these tokens to push updates to the extensions, potentially compromising developers’ systems.
Critical Risk of Leaked Tokens
According to Wiz security researcher Rami McCarthy, “A leaked VSCode Marketplace or Open VSX personal access token (PAT) can allow an attacker to distribute a malicious update to all users.” The vulnerability could have affected roughly 150,000 users, demonstrating the seriousness of these leaks.
Many extension publishers fail to consider that VS Code extensions, packaged as .vsix files, can be unzipped and inspected. This exposes hard-coded secrets, including API keys and authentication tokens. In total, Wiz identified over 550 secrets across 500+ extensions from hundreds of publishers, spanning 67 different types of sensitive credentials:
- AI provider secrets – including OpenAI, Gemini, Anthropic, XAI, DeepSeek, Hugging Face, and Perplexity
- Cloud services – such as AWS, Google Cloud, GitHub, Stripe, and Auth0
- Database credentials – like MongoDB, PostgreSQL, and Supabase
Among these, over 100 extensions leaked VS Code Marketplace PATs, impacting more than 85,000 installs. An additional 30 extensions exposed Open VSX Access Tokens with a combined install base of at least 100,000. Many of the affected extensions were themes.
With AI-powered VS Code forks like Cursor and Windsurf integrating Open VSX, extensions leaking tokens significantly increase the attack surface. In one notable case, a leaked PAT could have enabled attackers to target the workforce of a $30 billion Chinese corporation.
Microsoft Response
After responsible disclosure in March-April 2025, Microsoft revoked the leaked PATs and is introducing secret scanning to block extensions with embedded secrets and alert developers.
Recommendations for Users and Organizations
- Limit installed extensions and avoid unnecessary add-ons
- Carefully review extensions before downloading
- Evaluate the risks of enabling auto-updates
- Organizations should maintain an inventory of approved extensions and consider a centralized allowlist
TigerJack Campaign: Malicious Extensions
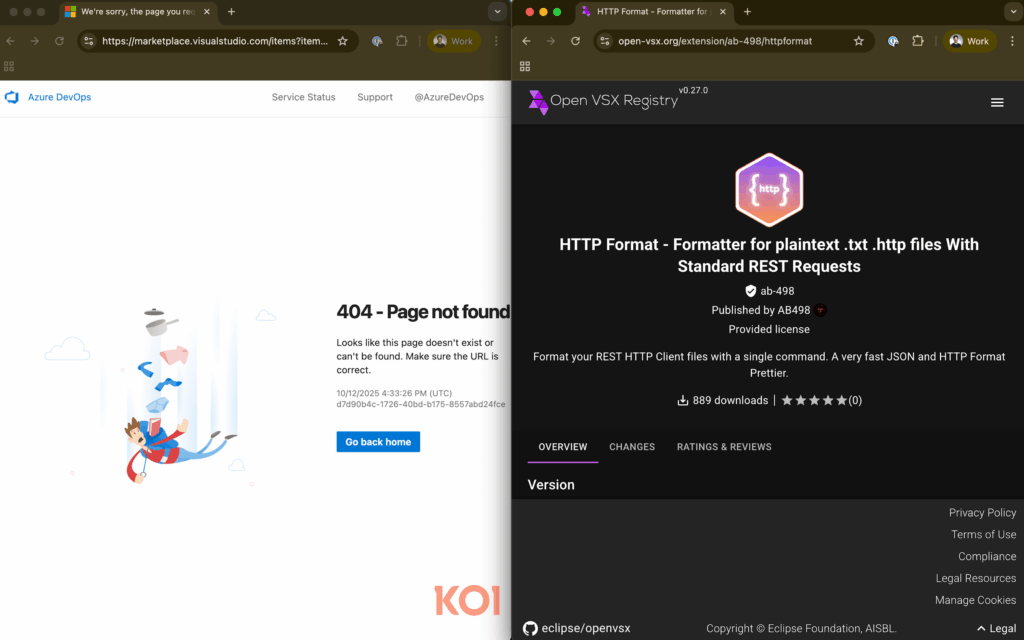
Koi Security exposed a threat actor, TigerJack, responsible for publishing at least 11 malicious-looking VS Code extensions since early 2025. Operating under aliases such as ab-498, 498, and 498-00, these extensions could steal source code, mine cryptocurrency, and install backdoors.
- C++ Playground – captures keystrokes almost in real-time to steal C++ files
- HTTP Format – secretly runs CoinIMP cryptocurrency miner
- Other extensions fetch arbitrary JavaScript every 20 minutes from a remote server, allowing dynamic malicious payloads, credential theft, ransomware deployment, and system monitoring
Many of these extensions initially appeared benign, only later modified to include malware, demonstrating a classic Trojan horse tactic. Even if removed from Microsoft’s VS Code Marketplace, these extensions remain available on Open VSX, highlighting the fragmented security landscape.