High profile organizations across South Asia, Southeast Asia, and East Asia are being targeted in an ongoing cyber campaign believed to be conducted by a Chinese linked threat group. The attacks have been running for several years and primarily focus on organizations that play a critical role in national infrastructure.
Security researchers from Palo Alto Networks Unit 42 have linked the activity to a previously unidentified threat cluster known as CL-UNK-1068. In this classification, the label “CL” represents cluster, while “UNK” indicates that the attackers’ exact motivation has not been fully confirmed.
Despite the uncertainty, analysts believe with moderate to high confidence that the primary purpose of the operation is cyber espionage, aimed at collecting sensitive data from strategic sectors.
Attack Targets Across Multiple Critical Industries
The campaign has targeted organizations working in several important industries including aviation, energy, government institutions, law enforcement, pharmaceuticals, technology companies, and telecommunications providers. These sectors are often considered critical infrastructure because of their importance to national security and economic stability.
Security researcher Tom Fakterman explained that the attackers rely on a diverse toolkit consisting of customized malware, altered open source utilities, and living off the land binaries. These tools allow attackers to remain hidden inside compromised networks while maintaining long term access.
Malware and Tools Used in the Intrusions
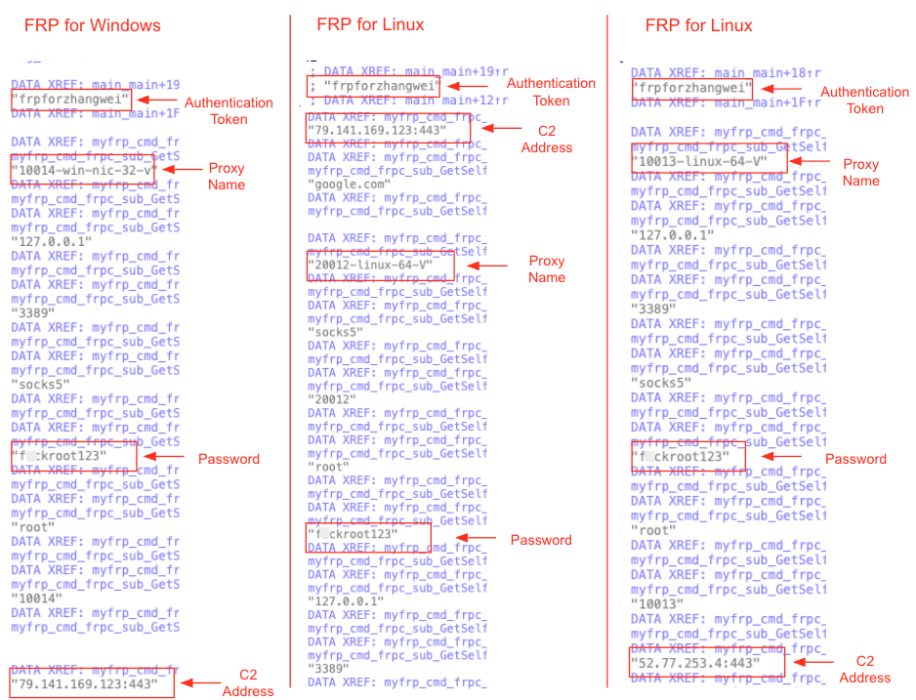
Investigators discovered that the attackers operate in both Windows and Linux environments using a combination of widely available tools and previously observed malware families.
Some of the tools involved include:
- Godzilla
- ANTSWORD
- Xnote
- Fast Reverse Proxy (FRP)
Both Godzilla and ANTSWORD function as web shells, giving attackers remote control over compromised servers. Meanwhile Xnote is a Linux backdoor that has been observed in cyber attacks since 2015. It was previously associated with another threat group known as Earth Berberoka, also referred to as GamblingPuppet, which targeted online gambling platforms.
How the Attack Chain Works
The typical attack sequence begins with the exploitation of vulnerable web servers. Once attackers gain access, they deploy web shells that allow them to execute commands remotely and move laterally across the network to other systems.
After establishing access, the attackers attempt to collect files from the Windows web server directory:
c:\inetpub\wwwroot
They specifically search for files with extensions such as:
- web.config
- .aspx
- .asmx
- .asax
- .dll
These files may contain credentials, configuration information, or security weaknesses that could help attackers expand their access.
The threat group also gathers additional data including browser history, bookmarks, spreadsheet files like XLSX and CSV, and database backup files stored on Microsoft SQL servers.
Unusual Data Exfiltration Technique
One interesting method observed during the attacks involves a creative approach to stealing data.
Instead of transferring files directly, attackers first compress the collected data using WinRAR. They then encode the archive into Base64 format using the command:
certutil -encode
After encoding the data, they run the type command to display the Base64 output directly in the web shell interface.
By converting the data into text and displaying it on the screen, attackers can copy the encoded content without performing an actual file transfer. Researchers believe this technique was used because the web shell allowed command execution but did not support direct file uploads or downloads.
Advanced Techniques for Stealthy Execution
The attackers were also observed using legitimate Python executables, including python.exe and pythonw.exe, to perform DLL side loading attacks. This method allows malicious DLL files to run while appearing to be part of legitimate software.
Among the tools deployed through this technique were:
- FRP, used to maintain persistent access
- PrintSpoofer, a privilege escalation tool
- ScanPortPlus, a custom Go based network scanning tool
Reconnaissance and Credential Theft
The threat group has been conducting reconnaissance activities for several years. As early as 2020, they used a custom .NET based tool called SuperDump to gather information about compromised systems.
More recent attacks show the group shifting to batch scripts that automatically collect system details and map the local network environment.
To steal credentials, attackers relied on a wide range of tools including:
- Mimikatz, used to extract passwords stored in memory
- LsaRecorder, which records login passwords by hooking authentication functions
- DumpItForLinux and Volatility Framework, used to obtain password hashes from memory
- SQL Server Management Studio Password Export Tool, which extracts stored database connection information from the file sqlstudio.bin
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


