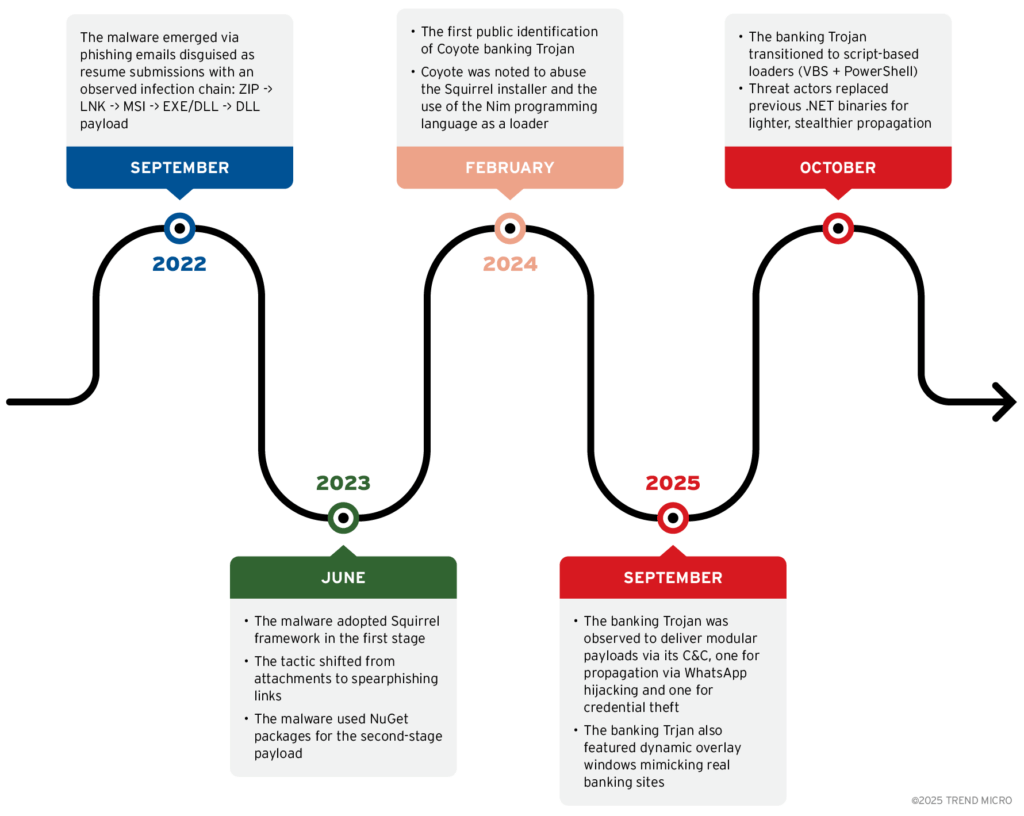
Cybersecurity researchers have uncovered a sophisticated banking malware campaign in Brazil involving a new threat called Maverick, which spreads via WhatsApp and targets banking users by hijacking browser sessions. The campaign shows strong links to a prior malware strain known as Coyote, though Maverick exhibits new propagation and remote control techniques.
How Maverick Spreads
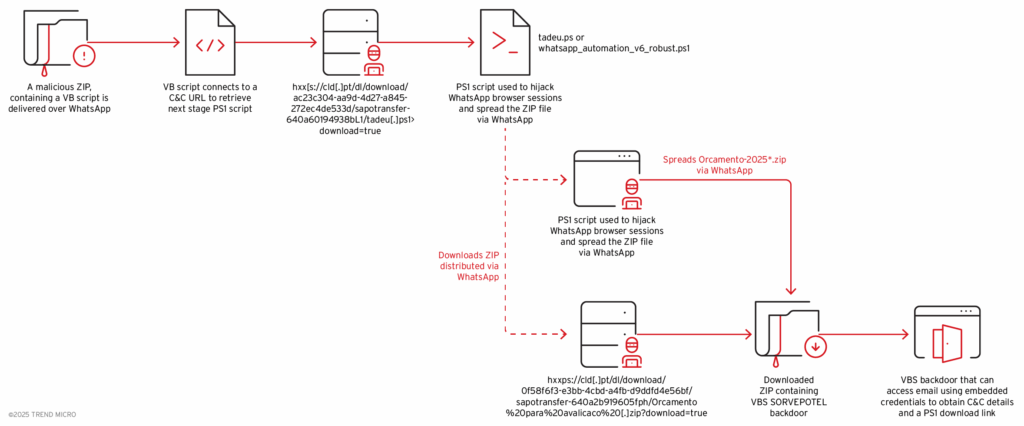
Maverick employs a two-component infection chain:
- SORVEPOTEL – a self-propagating malware distributed through WhatsApp Web, used to deliver a ZIP archive containing the Maverick payload.
- Maverick Payload – monitors browser tabs, intercepts banking websites, and executes phishing pages to steal credentials.
The malware spreads by tricking users into opening the ZIP file, which contains obfuscated scripts and commands that compromise the victim’s WhatsApp Web session. Once installed, it automatically distributes the malicious ZIP to all contacts in the user’s account.
Targeting Brazilian Banking Systems
Maverick specifically targets financial institutions in Latin America. The malware verifies the host location, ensuring the victim is in Brazil by checking time zone, language, region, and system settings before deploying the payload. Once active, it monitors active browser tabs and intercepts banking credentials.
The campaign also includes targeting hotels in Brazil, indicating a possible expansion of its scope beyond banking users.
Advanced Techniques for Stealth and Control
Maverick uses several advanced evasion and control techniques:
- Browser Hijacking: The malware copies legitimate Chrome profile data, including cookies and authentication tokens, enabling full access to WhatsApp Web without triggering alerts.
- Remote C2 Control: Threat actors can pause, resume, and monitor the malware in real-time, turning infected devices into dynamic bots.
- Automation: PowerShell scripts automate the distribution of malicious ZIP files, sending personalized messages to contacts.
- Email-based Commands: Uses IMAP access to terra.com.br email accounts to retrieve instructions from the attacker-controlled C2 server.
Supported Commands
Maverick provides a wide array of commands for attackers, including:
- Collect system information
- Execute cmd.exe and PowerShell commands
- Take screenshots
- List, copy, move, delete, or rename files
- Create folders
- Download and upload files
- Reboot or shutdown the system
- Update itself
- Check C2 server for new instructions
These capabilities make Maverick a highly flexible and dangerous threat for Brazilian users, particularly those relying on online banking and enterprise systems.
Regional Impact and Cybercriminal Links
Brazil has over 148 million active WhatsApp users, making it a prime target. Cybersecurity experts suggest that Maverick is operated by the Water Saci threat group, which likely shares ties with the Coyote malware ecosystem. This indicates a growing sophistication and regional focus in Brazilian cybercrime operations.
“The shift from traditional payloads to exploiting legitimate browser profiles and messaging platforms demonstrates the attackers’ strategic evolution,” Trend Micro noted.


