An advanced persistent threat (APT) group known as WIRTE has been linked to cyberattacks targeting government and diplomatic entities across the Middle East since 2020. The group deploys a previously undocumented malware suite called AshTag, designed for espionage and intelligence collection. Palo Alto Networks Unit 42 is tracking this cluster under the codename Ashen Lepus.
Evidence collected from VirusTotal indicates that WIRTE has recently expanded its operations to Oman and Morocco, in addition to earlier targets including the Palestinian Authority, Jordan, Iraq, Saudi Arabia, and Egypt. The campaign is notable for its persistence, with attacks continuing during the Israel-Hamas conflict and even after the October 2025 Gaza ceasefire. Unit 42 reports that Ashen Lepus has deployed newly developed malware variants while conducting hands-on operations within victim environments.
WIRTE overlaps with the Arabic-speaking Gaza Cyber Gang (also known as Blackstem, Extreme Jackal, Molerats, or TA402), a politically motivated threat cluster active since at least 2018. Unit 42 researchers highlight code overlaps and shared development resources between WIRTE and other subgroups like Molerats and APT-C-23 (Arid Viper or Renegade Jackal), suggesting coordinated tool development while maintaining operational independence.
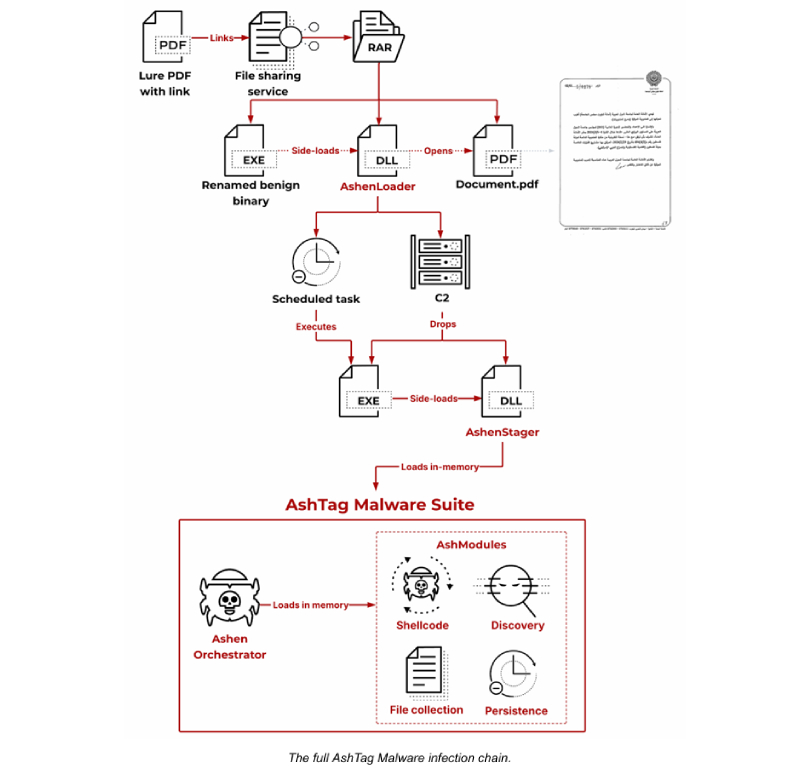
The attack chain begins with a decoy PDF used in phishing emails that tricks recipients into downloading a RAR archive from a file-sharing service. Extracting the archive triggers the deployment of AshTag through a renamed benign executable that sideloads a malicious DLL called AshenLoader. This loader opens the decoy PDF to maintain the ruse, while retrieving two additional components: a legitimate executable and AshenStager (stagerx64), which is sideloaded to launch the malware suite in memory to minimize forensic traces.
AshTag is a modular .NET backdoor that enables persistence, remote command execution, and communication through the AshenOrchestrator. Its modules provide:
- Process management and persistence
- Update and removal capabilities
- Screen capture
- File system exploration and management
- System fingerprinting
Unit 42 also observed hands-on data theft, where threat actors staged documents from victim email inboxes into C:\Users\Public and exfiltrated them to attacker-controlled servers using the Rclone utility. The primary focus appears to be diplomacy-related documents.
The campaign demonstrates a sustained espionage effort. Ashen Lepus continues active operations, highlighting a persistent commitment to intelligence collection over the past several years, particularly in environments lacking advanced detection capabilities.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


