Cybersecurity experts have closely monitored the development of XWorm malware, evolving it into a highly adaptable tool capable of executing a broad range of malicious operations on infected systems.
Trellix researchers Niranjan Hegde and Sijo Jacob explained, “XWorm’s architecture is modular, consisting of a core client and multiple specialized components known as plugins. Each plugin acts as an additional payload, designed to perform targeted harmful actions once the malware is active.”
First identified in 2022 and linked to a threat actor called EvilCoder, XWorm functions as a multi-purpose malware toolkit. Its capabilities include data exfiltration, keylogging, screen capture, system persistence, and even ransomware deployment. The malware is primarily spread via phishing campaigns and fake websites promoting malicious ScreenConnect installers.
Other tools associated with the malware developer include a .NET-based malware builder, the XBinder remote access trojan, and software that bypasses Windows User Account Control (UAC). Recently, development has been attributed to an online persona known as XCoder.
A report last month by Trellix highlighted evolving infection chains for XWorm, which leveraged Windows shortcut (LNK) files delivered through phishing emails. These files executed PowerShell commands that dropped a harmless TXT file alongside a deceptive executable mimicking Discord, ultimately triggering the malware.
XWorm also integrates sophisticated anti-analysis and anti-evasion techniques, detecting virtualized environments and halting execution to avoid detection. Its modular design allows external servers to issue commands for tasks such as system shutdown, file downloads, URL launches, and DDoS attacks.
Trellix emphasized, “The rapid adaptation of XWorm within the threat landscape underscores the importance of strong security measures to defend against evolving threats.”
Despite its growth, XWorm has faced setbacks. Notably, XCoder deleted their Telegram account in late 2024, casting uncertainty over the malware’s future. Nevertheless, threat actors have circulated a cracked version of XWorm 5.6, containing malware intended to compromise other operators.
This included attempts by unknown actors to distribute a trojanized XWorm RAT builder via GitHub, file-sharing services, Telegram channels, and YouTube, impacting over 18,459 devices worldwide. Other modifications include variants such as XSPY, a Chinese version, and the identification of a remote code execution (RCE) vulnerability exploitable by attackers with the C2 encryption key.
Although XCoder’s apparent departure suggested XWorm might be discontinued, Trellix reported that a threat actor named XCoderTools began offering XWorm 6.0 on cybercrime forums on June 4, 2025, for $500 lifetime access. The new version is described as fully re-coded with the RCE flaw fixed, though it is unclear if the original developer or a new actor is responsible.
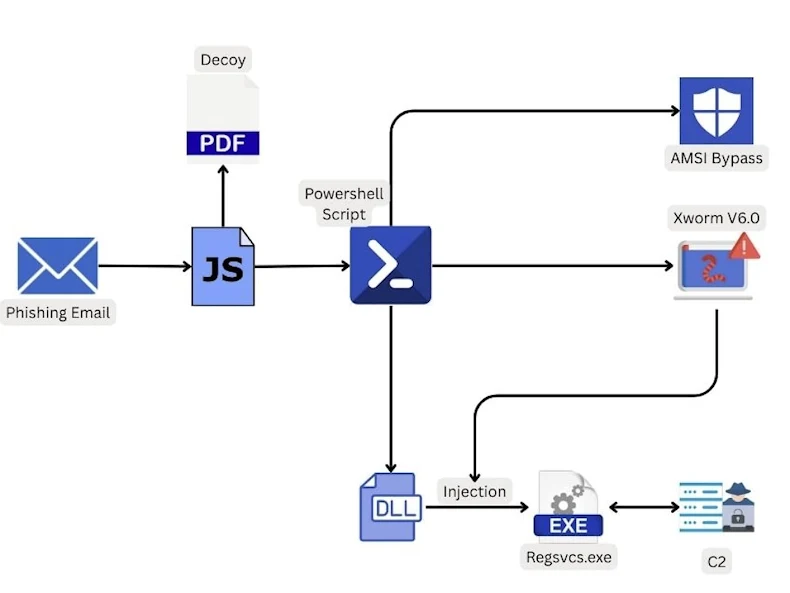
Current campaigns distributing XWorm 6.0 involve malicious JavaScript files in phishing emails. When opened, these display a decoy PDF while PowerShell executes in the background, injecting malware into legitimate Windows processes like RegSvcs.exe without detection.
XWorm 6.0 connects to its C2 server at 94.159.113[.]64 on port 4411 and includes a “plugin” command, enabling execution of more than 35 DLL payloads in memory for various tasks.
Trellix explained, “The C2 server sends a ‘plugin’ command with the SHA-256 hash of the plugin DLL and invocation arguments. The client verifies if the plugin already exists and, if not, requests it from the server. The plugin is then sent in base64 encoding, decoded, and loaded into memory.”
Some notable XWorm 6.x plugins include:
- RemoteDesktop.dll: Establishes a remote session on the victim machine
- WindowsUpdate.dll, Stealer.dll, Recovery.dll, merged.dll, Chromium.dll, SystemCheck.Merged.dll: Extracts Windows product keys, Wi-Fi passwords, and credentials from apps like FileZilla, Discord, Telegram, and MetaMask
- FileManager.dll: Provides filesystem access and manipulation
- Shell.dll: Executes hidden system commands
- Informations.dll: Gathers system details
- Webcam.dll: Records the victim and verifies machine authenticity
- TCPConnections.dll, ActiveWindows.dll, StartupManager.dll: Reports TCP connections, active windows, and startup programs
- Ransomware.dll: Encrypts files for cryptocurrency ransom (shares code with NoCry ransomware)
- Rootkit.dll: Installs a modified r77 rootkit
- ResetSurvival.dll: Ensures persistence after system reset via Windows Registry
XWorm 6.0 infections have also served as carriers for malware like DarkCloud Stealer, Hworm, Snake KeyLogger, Coin Miner, Pure Malware, ShadowSniff Stealer, Phantom Stealer, Phemedrone Stealer, and Remcos RAT.
Trellix noted, “Analysis of DLL files on VirusTotal revealed multiple XWorm V6.0 builders already infected with XWorm, indicating operators themselves were compromised.”
The return of XWorm 6.0, armed with versatile plugins for keylogging, credential theft, and ransomware, is a stark reminder that no malware threat ever truly disappears.