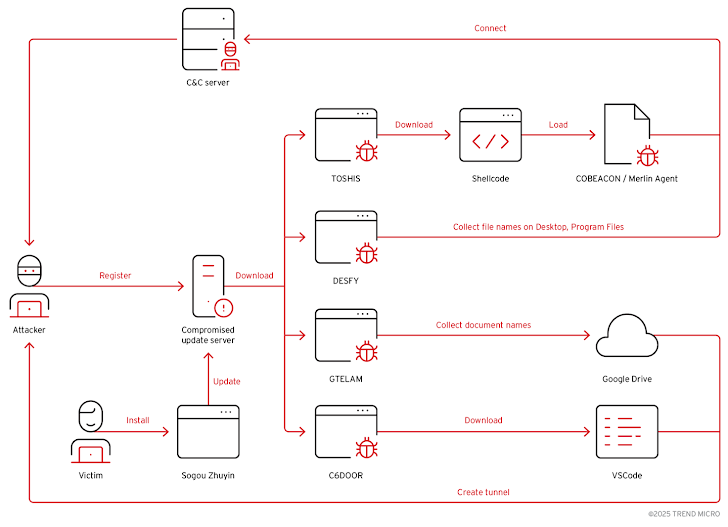
An abandoned update server once linked to the Sogou Zhuyin Input Method Editor (IME) has been hijacked by threat actors in a large-scale espionage campaign. The attackers exploited the server to distribute multiple malware families including C6DOOR and GTELAM, primarily targeting users across East Asia.
According to Trend Micro researchers Nick Dai and Pierre Lee, the operation relied on hijacked update mechanisms and fake cloud storage or login portals to trick victims into installing malware, enabling the collection of sensitive data.
This campaign, identified in June 2025 and codenamed TAOTH, has focused on dissidents, journalists, researchers, and technology leaders in Taiwan, China, Hong Kong, Japan, South Korea, and overseas Taiwanese communities. Taiwan has been the hardest hit, accounting for 49% of cases, followed by Cambodia (11%) and the United States (7%).
Abandoned Domain Exploitation
In October 2024, attackers gained control of the expired domain sogouzhuyin[.]com, originally tied to the now-defunct IME service which stopped updates in 2019. By November 2024, they began distributing malicious updates, affecting several hundred victims.
The compromised server delivered multiple malware families including GTELAM, C6DOOR, DESFY, and TOSHIS. Each tool served different purposes such as remote access, espionage, and information theft. To avoid detection, attackers also used third-party cloud services, including Google Drive, to hide malicious traffic and exfiltrate stolen data.
Victims were often misled into downloading the official Sogou Zhuyin installer from sources such as the Traditional Chinese Wikipedia page, which by March 2025 had been altered to redirect users to dl[.]sogouzhuyin[.]com. While the installer itself was harmless, the auto-update process was compromised. After installation, the binary ZhuyinUp.exe retrieved an update configuration file from srv-pc.sogouzhuyin[.]com/v1/upgrade/version, which triggered the malware download.
Malware Families Used in the Campaign
- TOSHIS (Detected Dec 2024): A loader designed to fetch second-stage payloads such as Cobalt Strike or the Merlin agent. Believed to be a variant of Xiangoop, associated with Tropic Trooper.
- DESFY (Detected May 2025): Spyware that collects file names from Desktop and Program Files directories.
- GTELAM (Detected May 2025): Spyware that collects file metadata with extensions like PDF, DOC, XLS, PPT, and uploads results to Google Drive.
- C6DOOR: A custom Go-based backdoor using HTTP and WebSockets for command-and-control. It can gather system information, execute commands, manage files, capture screenshots, enumerate processes, and inject shellcode. Embedded Simplified Chinese characters in the code suggest a Chinese-speaking threat actor.
Trend Micro notes the attackers seemed to remain in a reconnaissance phase, inspecting victim systems and, in some cases, using tools like Visual Studio Code to establish covert tunnels.
Phishing Campaigns and Distribution
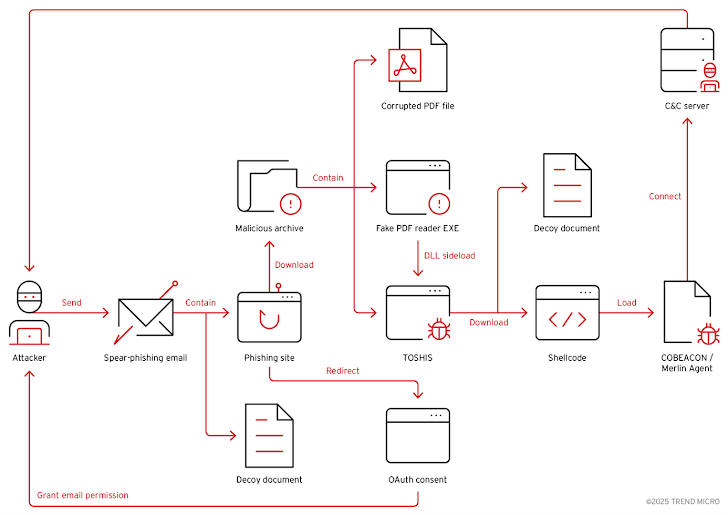
In addition to the compromised update chain, TOSHIS was also spread via phishing websites. These campaigns primarily targeted East Asia, but evidence shows spillover into the U.S. and Norway.
Attackers adopted a dual strategy:
- Fake login pages disguised as coupon or PDF reader services, tricking victims into granting OAuth access to attacker-controlled apps.
- Fake Tencent Cloud StreamLink pages that distributed malicious ZIP archives containing TOSHIS.
These phishing lures often included booby-trapped URLs and decoy documents to trigger a multi-stage attack sequence, enabling DLL side-loading or unauthorized mailbox access through OAuth prompts.
Connections to ITOCHU and Persistent Espionage
Trend Micro researchers found infrastructure and tool overlaps between TAOTH and activity previously linked to ITOCHU, suggesting a persistent and well-resourced espionage group with an emphasis on reconnaissance, email abuse, and long-term surveillance.
Security Recommendations
To defend against such threats, organizations should:
- Regularly audit and remove end-of-support software.
- Closely review permissions before granting access to cloud applications.
- Monitor suspicious network activities tied to abandoned domains.
“The Sogou Zhuyin operation shows how abandoned infrastructure can become a powerful espionage tool,” said Trend Micro. “While reconnaissance was the primary objective, spear-phishing attacks are ongoing and remain a high risk for targeted organizations.”
| Type | Value | Description / Usage |
|---|---|---|
| Domain | sogouzhuyin[.]com | Hijacked abandoned domain used for distributing malware updates |
| Domain | dl[.]sogouzhuyin[.]com | Malicious domain redirecting victims to download infected installer |
| Domain | srv-pc.sogouzhuyin[.]com | Domain used in update chain to fetch malicious configuration file |
| File | ZhuyinUp.exe | Updater binary abused in the auto-update process to trigger malware download |
| Malware Family | TOSHIS | Loader used to deliver Cobalt Strike, Merlin agent, or backdoors; variant of Xiangoop |
| Malware Family | DESFY | Spyware that collects filenames from Desktop and Program Files |
| Malware Family | GTELAM | Spyware that collects filenames (PDF, DOC, DOCX, XLS, XLSX, PPT, PPTX) and exfiltrates via Google Drive |
| Malware Family | C6DOOR | Go-based backdoor using HTTP/WebSockets for C2, supports file ops, screenshots, shellcode injection |
| C2 Infrastructure | Google Drive | Used for data exfiltration and hiding malicious traffic |
| Phishing Vector | Fake login pages (free coupons, PDF readers) | OAuth abuse for attacker-controlled apps |
| Phishing Vector | Fake Tencent Cloud StreamLink pages | Used to distribute ZIP archives containing TOSHIS |
| Phishing Vector | Booby-trapped URLs + decoy documents | Trigger multi-stage attack sequence (DLL side-loading, OAuth mailbox compromise) |