UAT-9921 Deploys VoidLink Malware Against Technology and Financial Sectors
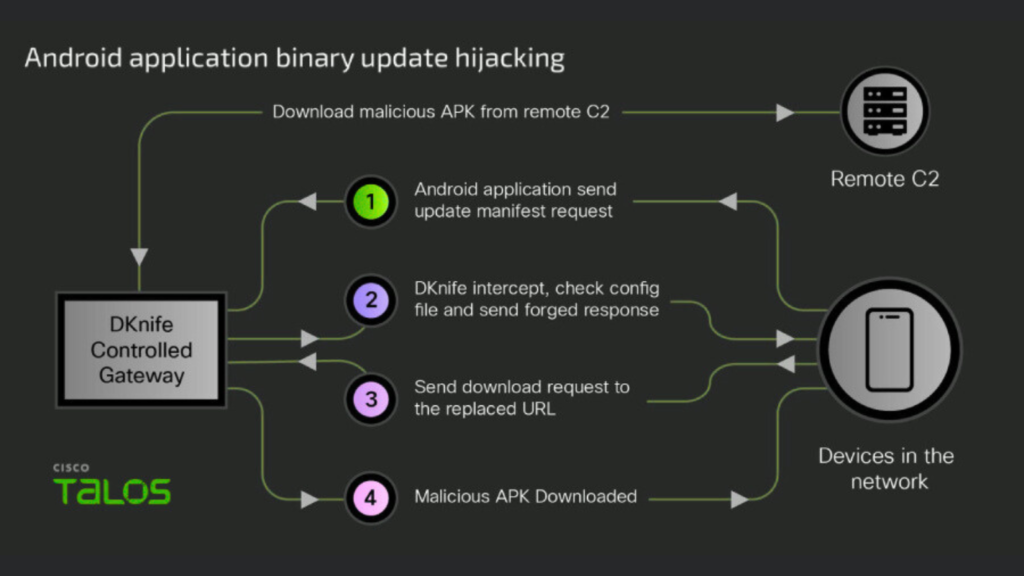
A previously unknown threat actor, tracked as UAT-9921, has been linked to sophisticated campaigns targeting technology and financial services organizations. The adversary employs a modular malware framework named VoidLink, capable of long term, stealthy access across Linux and Windows systems, according to findings by Cisco Talos. VoidLink demonstrates advanced capabilities, including kernel level rootkits, on-demand plugin compilation, and […]
UAT-9921 Deploys VoidLink Malware Against Technology and Financial Sectors Read More »