Cybersecurity experts have revealed a new AI-assisted malware strain named Slopoly, reportedly used by the financially motivated threat actor Hive0163 to maintain long-term access in ransomware attacks.
IBM X-Force researcher Golo Mühr commented, “Although still relatively unsophisticated, AI-generated malware like Slopoly demonstrates how easily attackers can leverage artificial intelligence to accelerate malware development.”
Overview of Hive0163 Operations
Hive0163 is known for large-scale extortion campaigns involving ransomware and data theft. The group commonly uses a range of malicious tools, including:
- NodeSnake
- Interlock RAT
- JunkFiction loader
- Interlock ransomware
In a recent incident from early 2026, Hive0163 deployed Slopoly in the post-exploitation phase to sustain persistent access on a compromised server for over a week.
How Slopoly Functions
Slopoly is delivered as a PowerShell script, likely installed under:
C:\ProgramData\Microsoft\Windows\Runtime\
Persistence is achieved via a scheduled task named “Runtime Broker.”
Evidence suggests that Slopoly was developed with the assistance of a large language model (LLM), indicated by:
- Extensive code comments and logging
- Accurate variable names
- Descriptions identifying it as a “Polymorphic C2 Persistence Client”
However, the malware itself is not fully polymorphic, as it cannot modify its code during execution. Instead, the builder generates multiple clients with randomized configuration values and function names, a common practice in malware development.
The script functions as a backdoor with the following capabilities:
- Sends system heartbeat messages to a C2 server every 30 seconds
- Polls for new commands every 50 seconds
- Executes commands via
cmd.exeand relays results back to the server
The exact types of commands executed within the compromised environment remain unknown.
Initial Infection and Attack Techniques
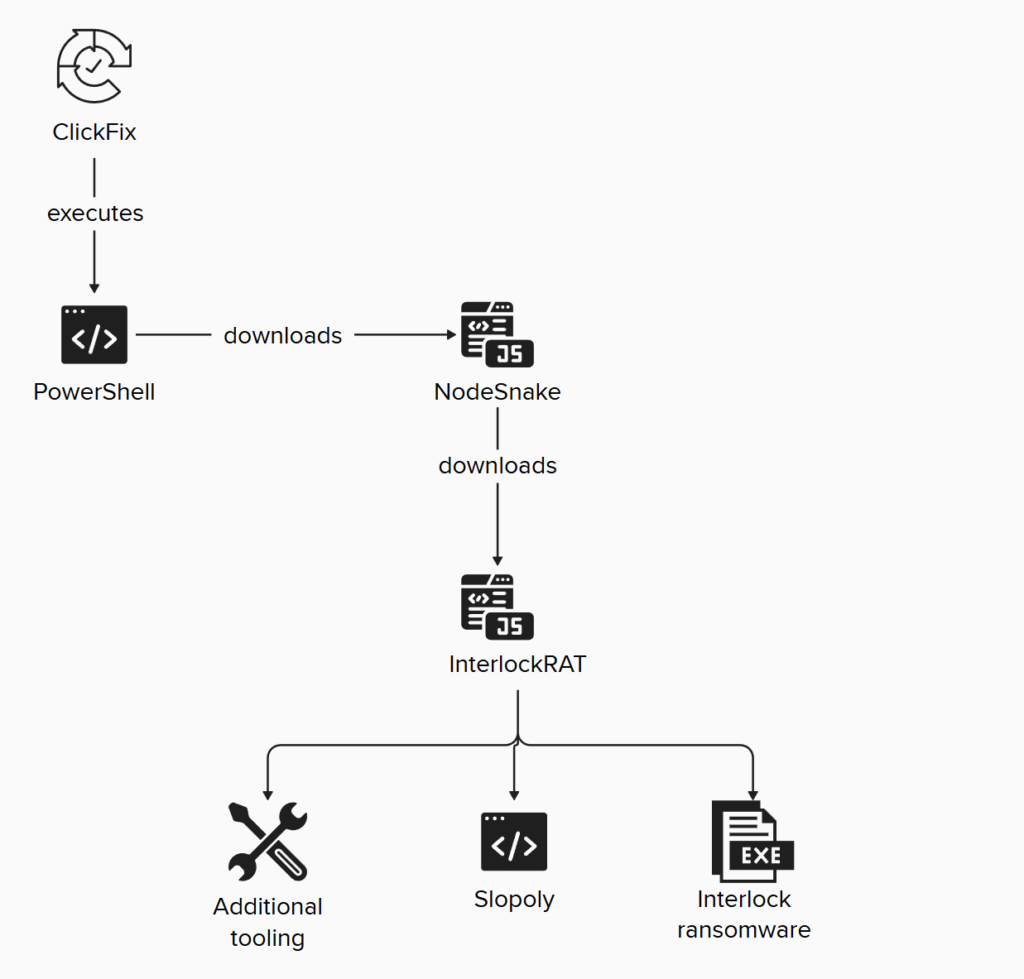
The attack leveraged a social engineering tactic called ClickFix, tricking victims into executing a PowerShell command. This downloaded NodeSnake, which runs shell commands, maintains persistence, and launches further components like Interlock RAT.
Hive0163 frequently uses:
- Malvertising campaigns
- Initial access brokers such as TA569 (SocGholish) and TAG-124 (KongTuke / LandUpdate808)
The malware framework supports multiple platforms and languages including PowerShell, PHP, C/C++, Java, and JavaScript for both Windows and Linux. It enables functionalities such as:
- Reverse shells
- SOCKS5 proxy tunnels
- Delivery of additional payloads, including Interlock ransomware and Slopoly
AI-Assisted Malware: A Growing Trend
Slopoly joins other AI-generated malware such as VoidLink and PromptSpy, highlighting how threat actors are leveraging AI to reduce development time and scale attacks.
IBM X-Force emphasized: “AI-generated malware may not be technically advanced, but it disproportionately empowers attackers by accelerating the timeline for developing and deploying attacks.”
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


